Every month, the headlines provide us with a stark reminder that cybersecurity is a continuously increasing threat. According to the Identity Theft Resource Center (ITRC), data breaches have increased by double digits since 2021.
- The average cost of a data breach was $4.24M in 2021, the highest on record – IBM
- The average time to identify a breach in 2021 was 212 days – IBM
- 68% of business leaders feel their cybersecurity risks are increasing – Accenture
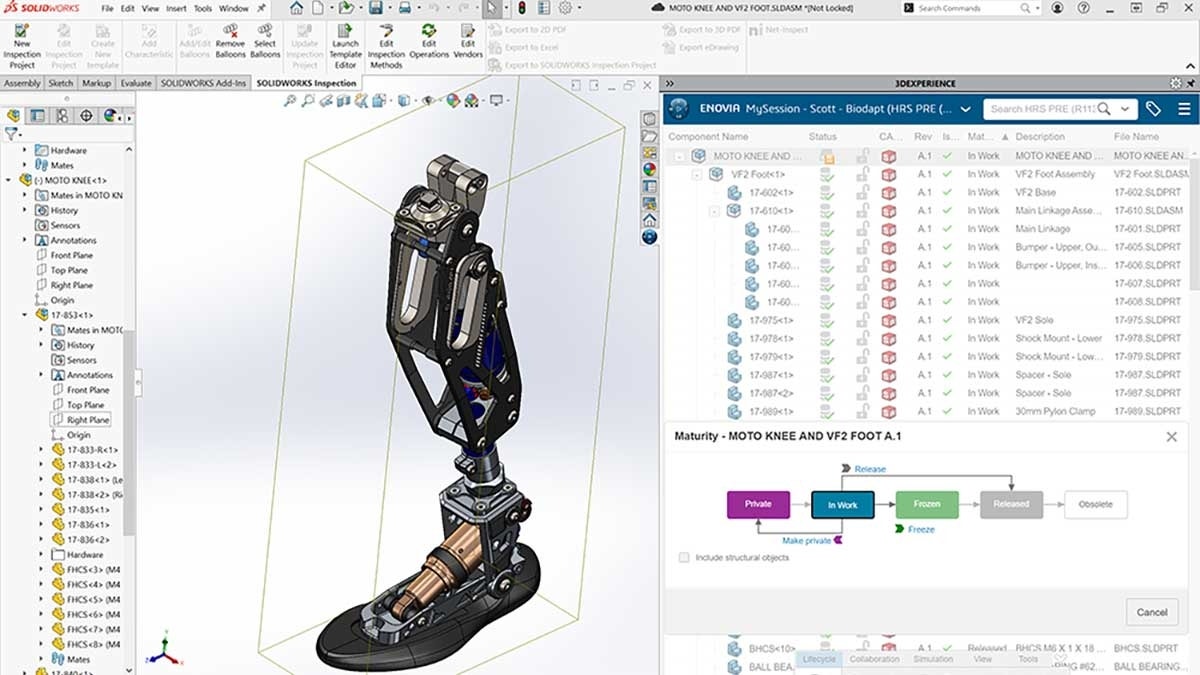
The core competencies of Hawk Ridge Systems for the last 25 years have been primarily focused on the SOLIDWORKS and Dassault Systèmes ecosystem application layer and above—implementation, training, and best-in-class support. However, a jack of all trades often is a master of none, and in recent years we’ve seen many of our customers need to migrate many (if not all) of their applications to the cloud. As a result of this need, we partnered with Jolera in 2020 as our managed service provider—to offer our customers optimal expertise and support around all things Azure cloud infrastructure, IT, and security.
Our IT and Security Service Offerings
At the core of our security offering is a proprietary Extended Detection and Response (XDR) platform. A fully managed solution integrated with industry-leading security products, services, and threat intelligence feeds to ensure the best tools and support experts protect environments—leveraging the following components:
- Extended Detection and Response (XDR): correlates environmental activity to threat intelligence to find active threats
- Endpoint Detection and Response (EDR) powered by SentinelOne: provides instant protection against cyber threats in an environment
- Vulnerability Detection Response (VDR) powered by Qualys: provides instructions on how to remediate weaknesses
- Cybersecurity Incident Response (CIR) powered by Jolera: 911 support in the events of critical security emergencies
Watch the Webinar
To learn more about the importance of IT security, threat detection, and the evolving threat landscape, watch this on-demand webinar with our partner, Jolera.
Final Thoughts
Though security is always a top priority in our Product Data Management (PDM) and Product Lifecycle Management (PLM) projects, extending this layer of protection across other enterprise workloads is equally important. Our team can assist with any of your organization’s IT challenges or if you’re looking for a new managed service provider.
Contact us for a discovery consultation to hear more.